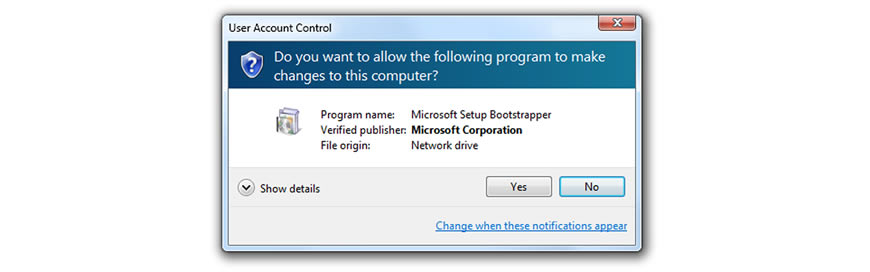
A new major vulnerability has been discovered that allows anyone to gain privilege escalation access to windows. This can be a major issue as normally the user has to be an administrator and allow escalated access to the computer. This vulnerability was discovered in Windows Task Scheduler.
Here are the specifics of the vulnerability "The Microsoft Windows task scheduler SchRpcSetSecurity API contains a vulnerability in the handling of ALPC, which can allow an authenticated user to overwrite the contents of a file that should be protected by filesystem ACLs. This can be leveraged to gain SYSTEM privileges. We have confirmed that the public exploit code works on 64-bit Windows 10 and Windows Server 2016 systems. We have also confirmed compatibility with 32-bit Windows 10 with minor modifications to the public exploit code. Compatibility with other Windows versions is possible with further modifications.
This vulnerability is being exploited in the wild."